Documentation Index
Fetch the complete documentation index at: https://help.skillsdb.com/llms.txt
Use this file to discover all available pages before exploring further.
NameID, firstName, lastName), and providing your App Federation Metadata URL back to SkillsDB.Overview
This guide walks Microsoft Entra ID (Azure AD) administrators through the steps required to integrate SkillsDB with their organization’s identity provider via SAML 2.0 Single Sign-On (SSO). Once configured, users can sign in to SkillsDB using their existing corporate credentials — without a separate SkillsDB password. Setup is a two-way exchange between two parties:- SkillsDB Support provides the SAML endpoint URLs (Identifier, Reply URL, and Sign on URL) that the customer must paste into the Entra enterprise application.
- The customer creates the Entra enterprise application, configures SAML, and returns either the App Federation Metadata URL (preferred) or, if that is not available, an x509 certificate plus the IdP SSO URL and IdP Entity ID.
Prerequisites
Before you begin, make sure you have:- Permission level: Microsoft Entra administrator access with permission to create enterprise applications
- Setup requirement: A Tenant URL and Secret Token request initiated with SkillsDB Support — Support will deliver the SAML endpoint URLs in a shared file once the request is processed
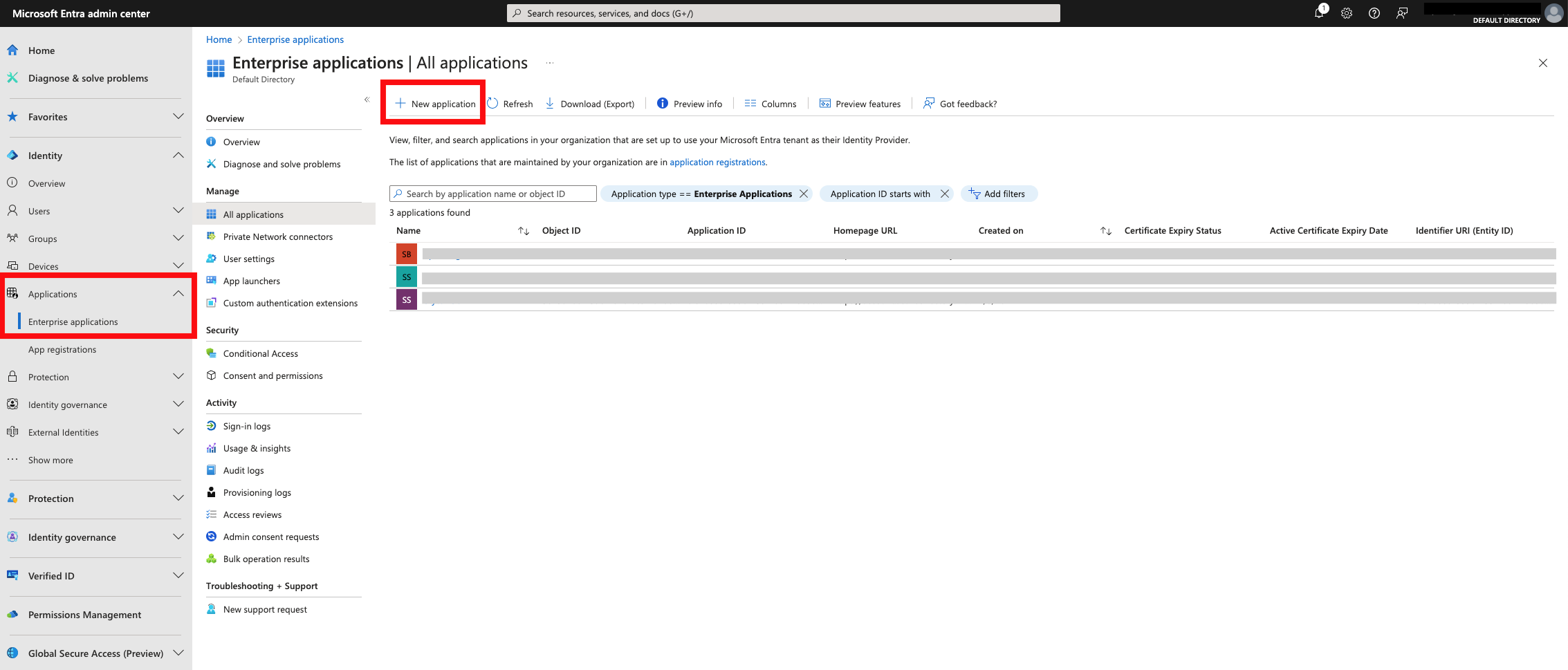
- Access requirement: The Microsoft Entra admin center at Identity > Applications > Enterprise applications
How to create the Entra enterprise application
Open Enterprise applications in Entra
Create your own application
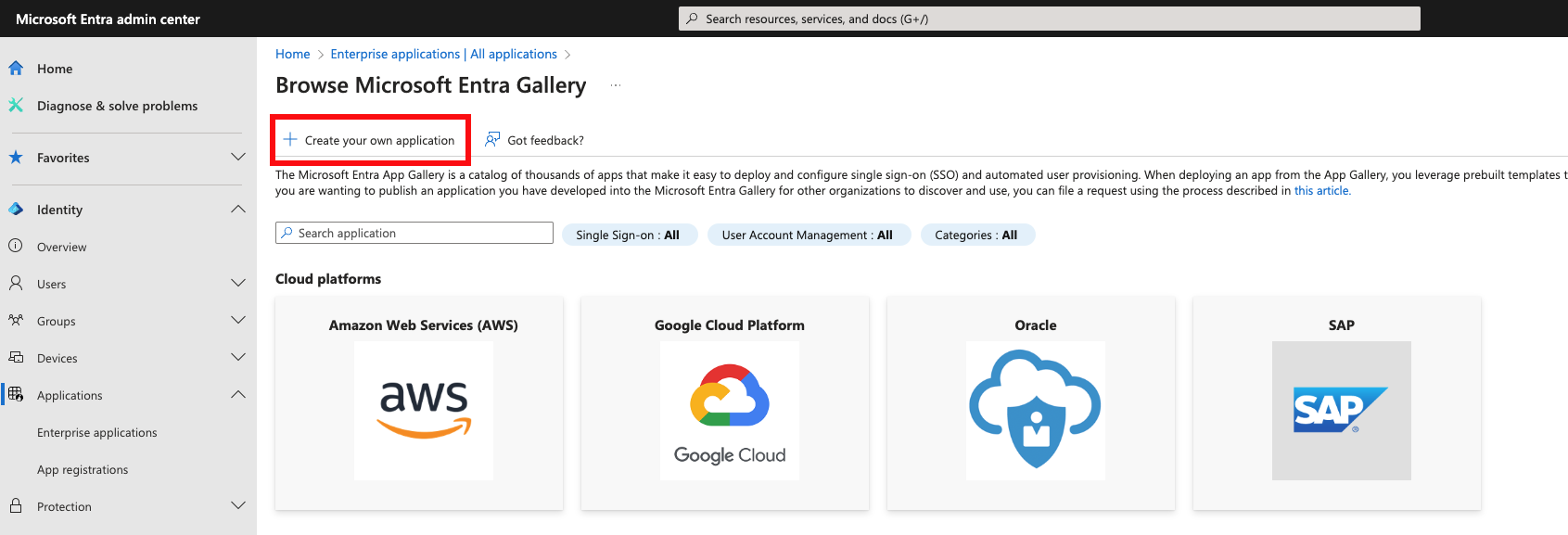
Name and register the application
SkillsDB), select Integrate any other application you don’t find in the gallery (Non-gallery), and select Create.How SkillsDB shares the SAML endpoint URLs
SkillsDB Support delivers the SAML endpoint URLs to your IT team in a text file. The file is uploaded to Google Drive and shared with the email addresses you provide; a link is also sent over email. The file contains three URLs in this format:https://test.stytch.com/* rather than https://login.skillsdb.com/*. SkillsDB Support will send the correct values for your environment.How to configure SAML in the enterprise application
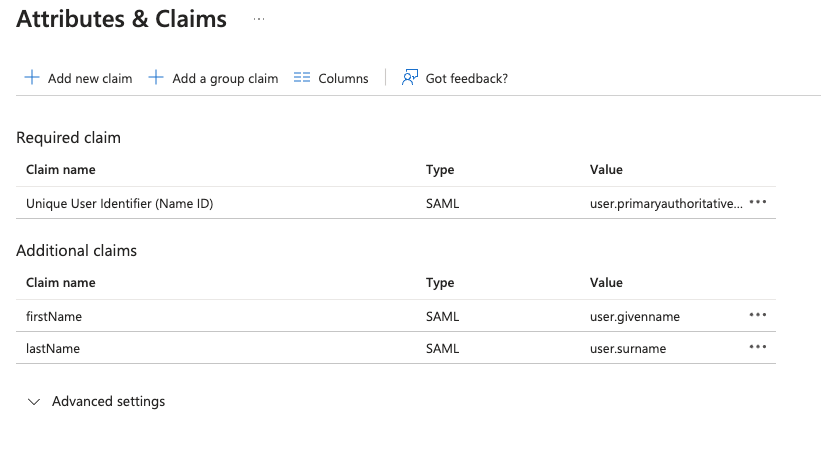
With the URLs from SkillsDB Support in hand, configure the Basic SAML Configuration section of your enterprise application.Edit Basic SAML Configuration
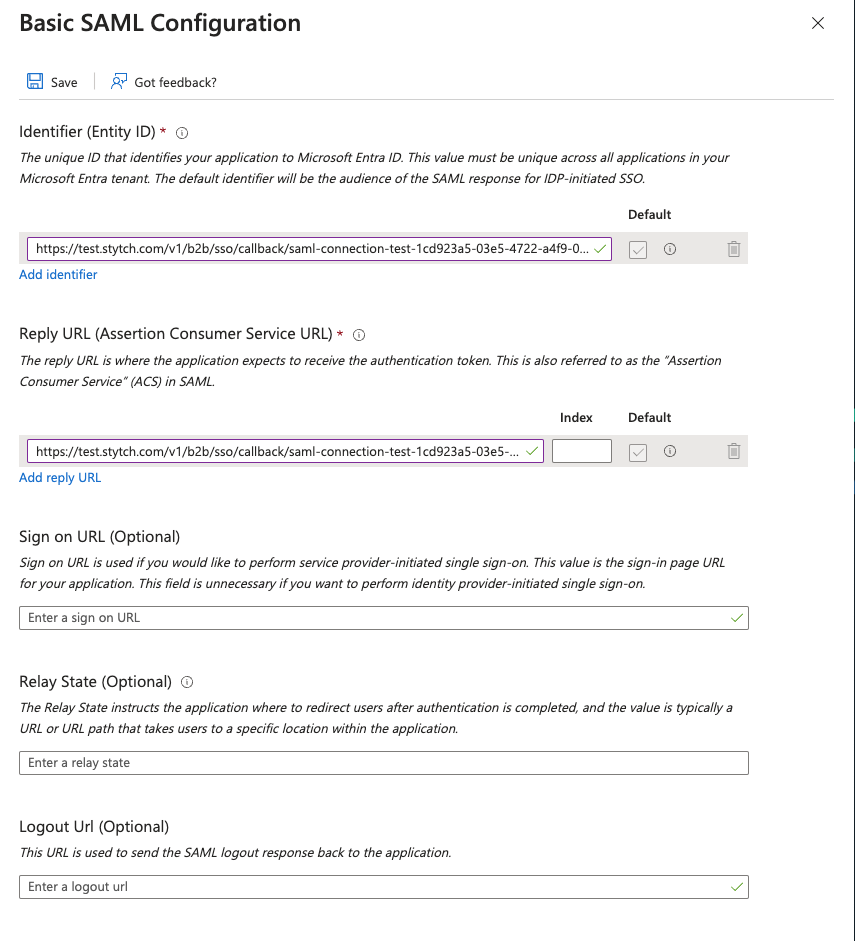
Paste the SkillsDB URLs
- Identifier (Entity ID) — the SkillsDB callback URL
- Reply URL (Assertion Consumer Service URL) — the same SkillsDB callback URL
- Sign on URL — the SkillsDB sign-on URL
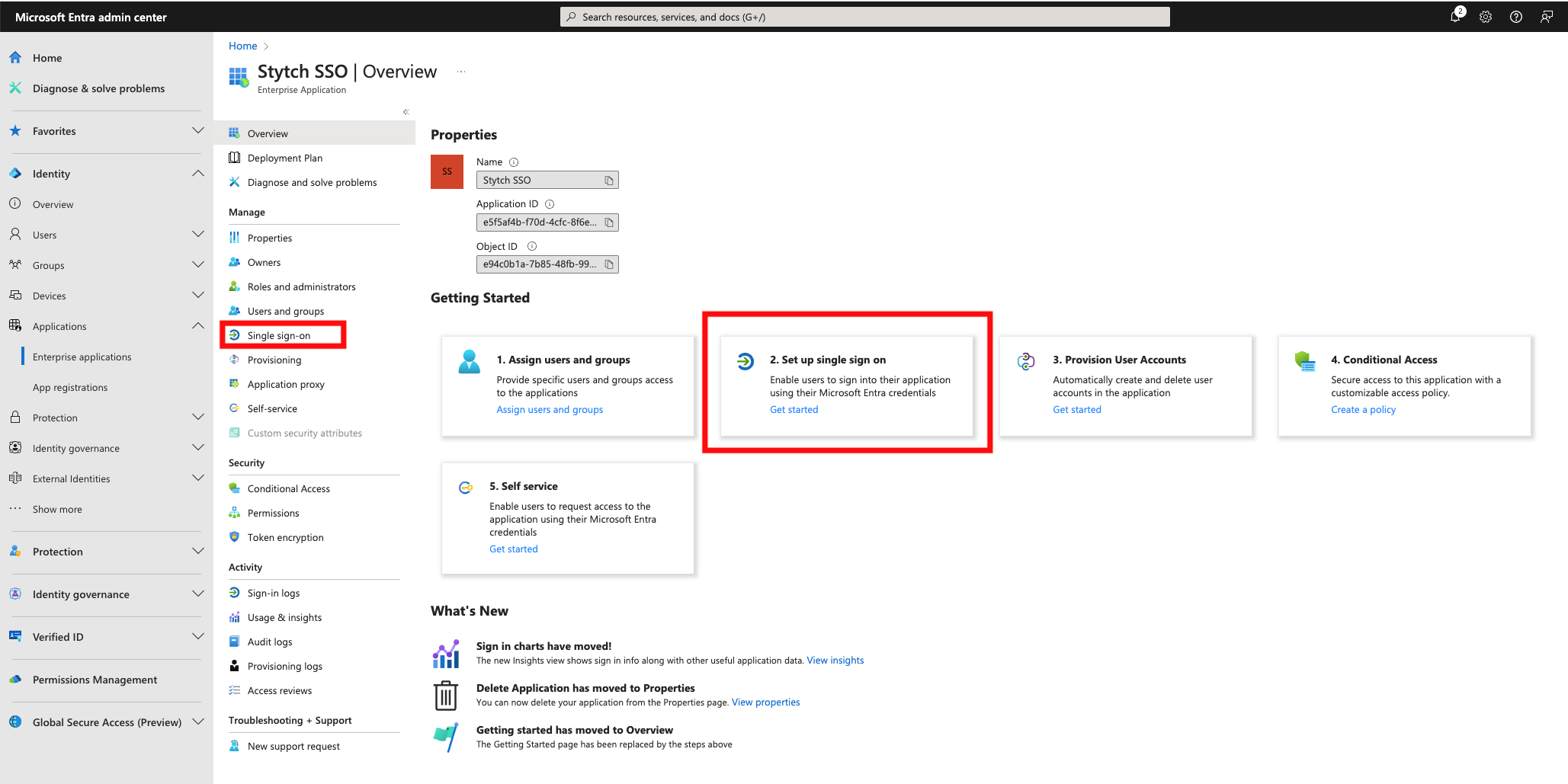
How to configure attributes and claims
SkillsDB requires three SAML claims to identify and create users: a unique email identifier (NameID), firstName, and lastName.
Update the Unique User Identifier
user.primaryauthoritativeemail.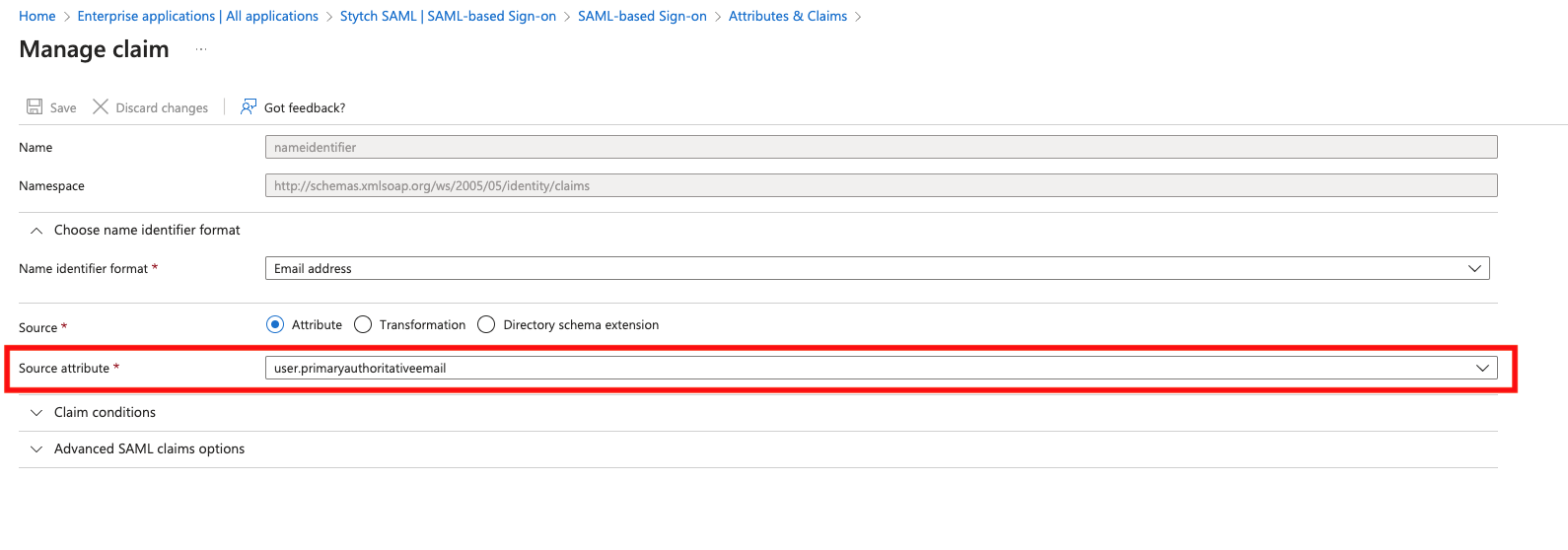
Adding optional custom attributes
If your organization needs to send additional attributes (for example,Department or JobTitle), add them in the same Attributes & Claims window:
- Select + Add new claim
- Enter a Name for the claim (for example,
Department) - Set the Source attribute to the corresponding Entra ID user property
- Save
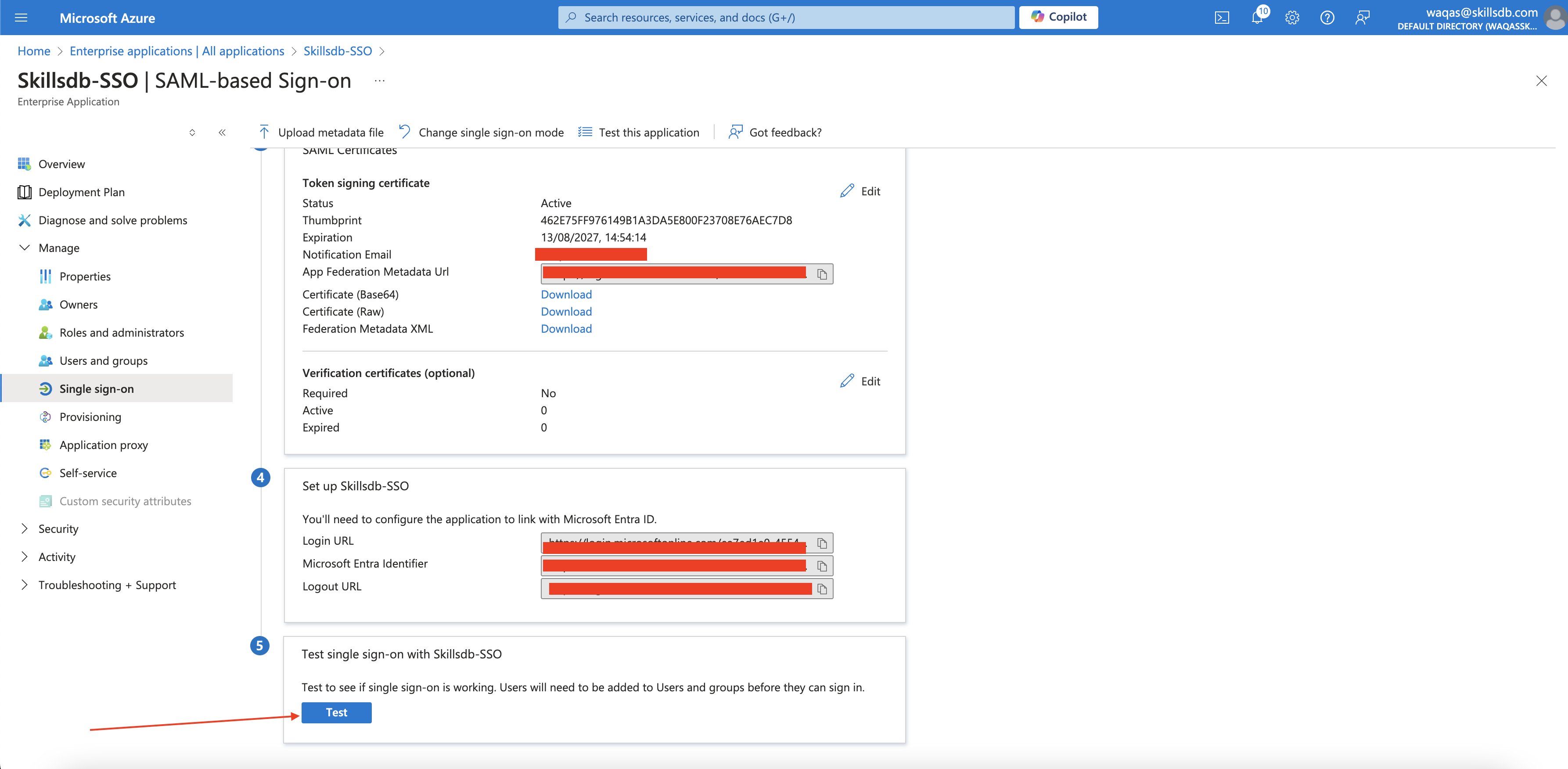
How to provide identity provider metadata to SkillsDB
After SAML is configured, SkillsDB needs your identity provider’s metadata to verify SAML assertions. There are two ways to deliver this — the App Federation Metadata URL is strongly preferred.Option 1: App Federation Metadata URL (preferred)
The App Federation Metadata URL is auto-rotating and self-contained. Use this option whenever it is available.Locate the App Federation Metadata URL
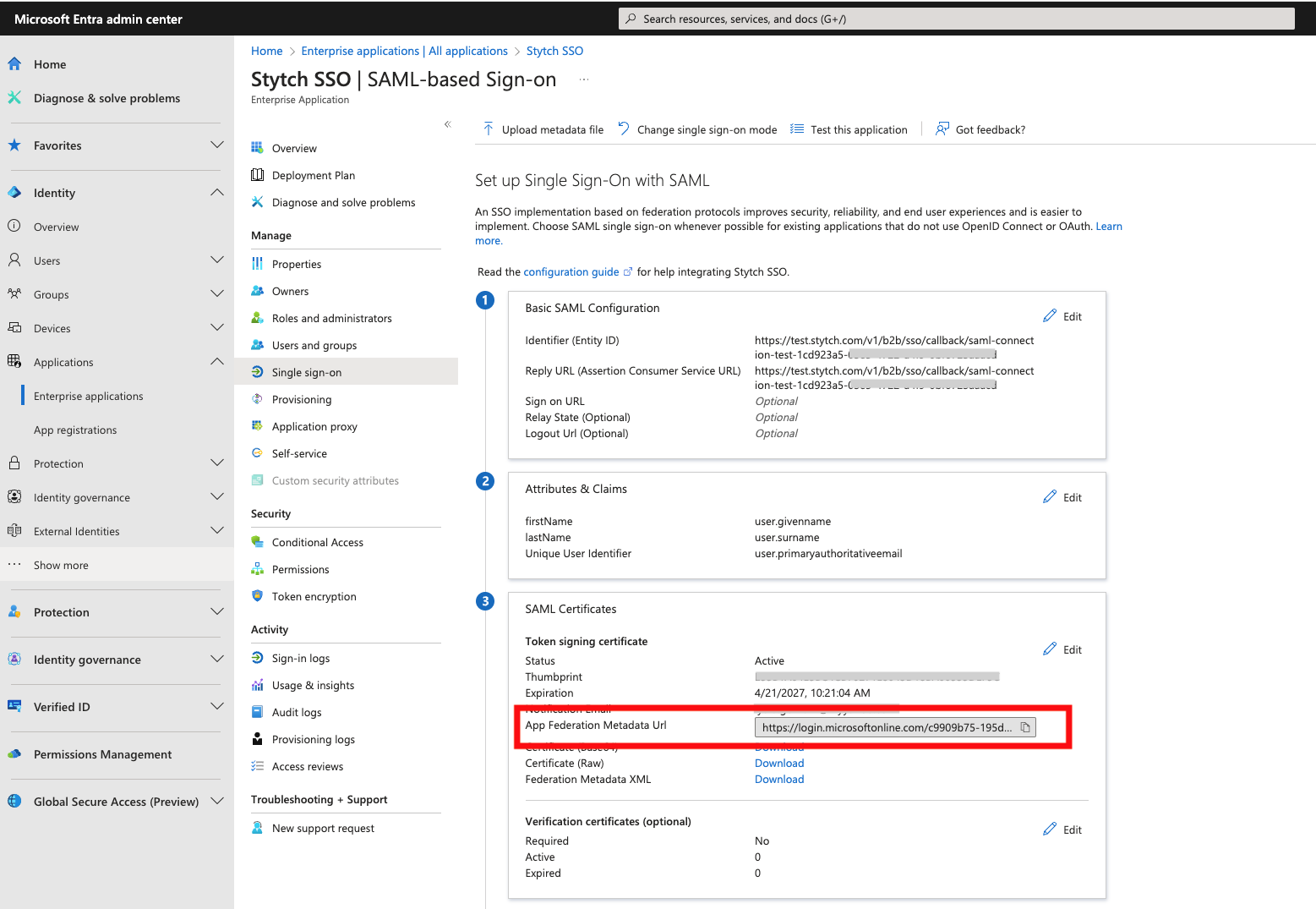
Share the URL with SkillsDB Support
- A shared OneDrive or Google Drive link
- A Google Meet or Microsoft Teams chat message
Option 2: x509 certificate (alternative)
Use this option only if your environment cannot expose the App Federation Metadata URL. The customer must provide:- The x509 certificate as an encrypted file
- The IdP SSO URL
- The IdP Entity ID
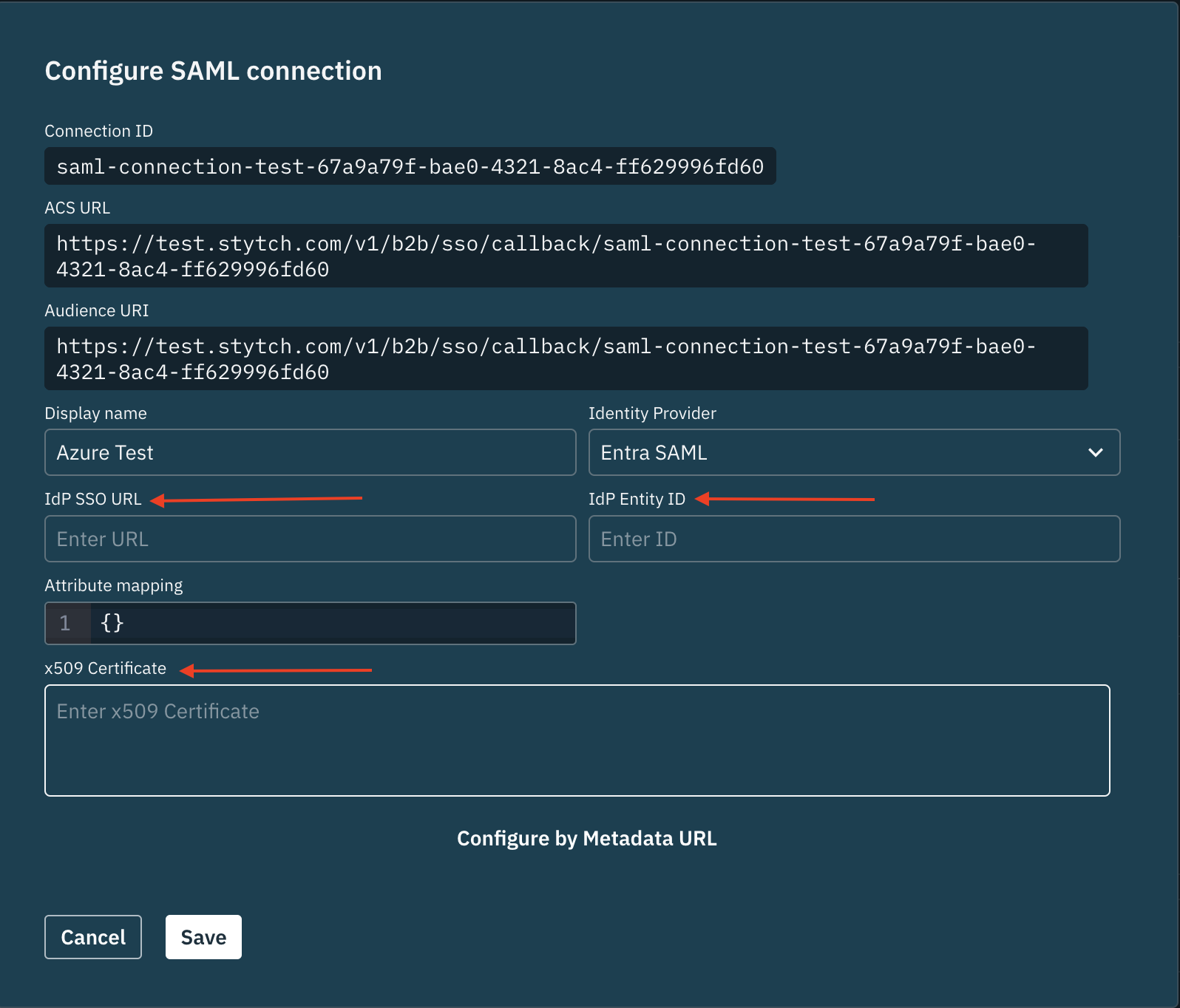 Encrypt the x509 certificate before sending it to SkillsDB. SkillsDB recommends 7-Zip with a password — exchange the password verbally over a meeting, never alongside the file.
Once SkillsDB Support decrypts the file, they apply it to your Stytch configuration along with the IdP SSO URL and IdP Entity ID.
Encrypt the x509 certificate before sending it to SkillsDB. SkillsDB recommends 7-Zip with a password — exchange the password verbally over a meeting, never alongside the file.
Once SkillsDB Support decrypts the file, they apply it to your Stytch configuration along with the IdP SSO URL and IdP Entity ID.
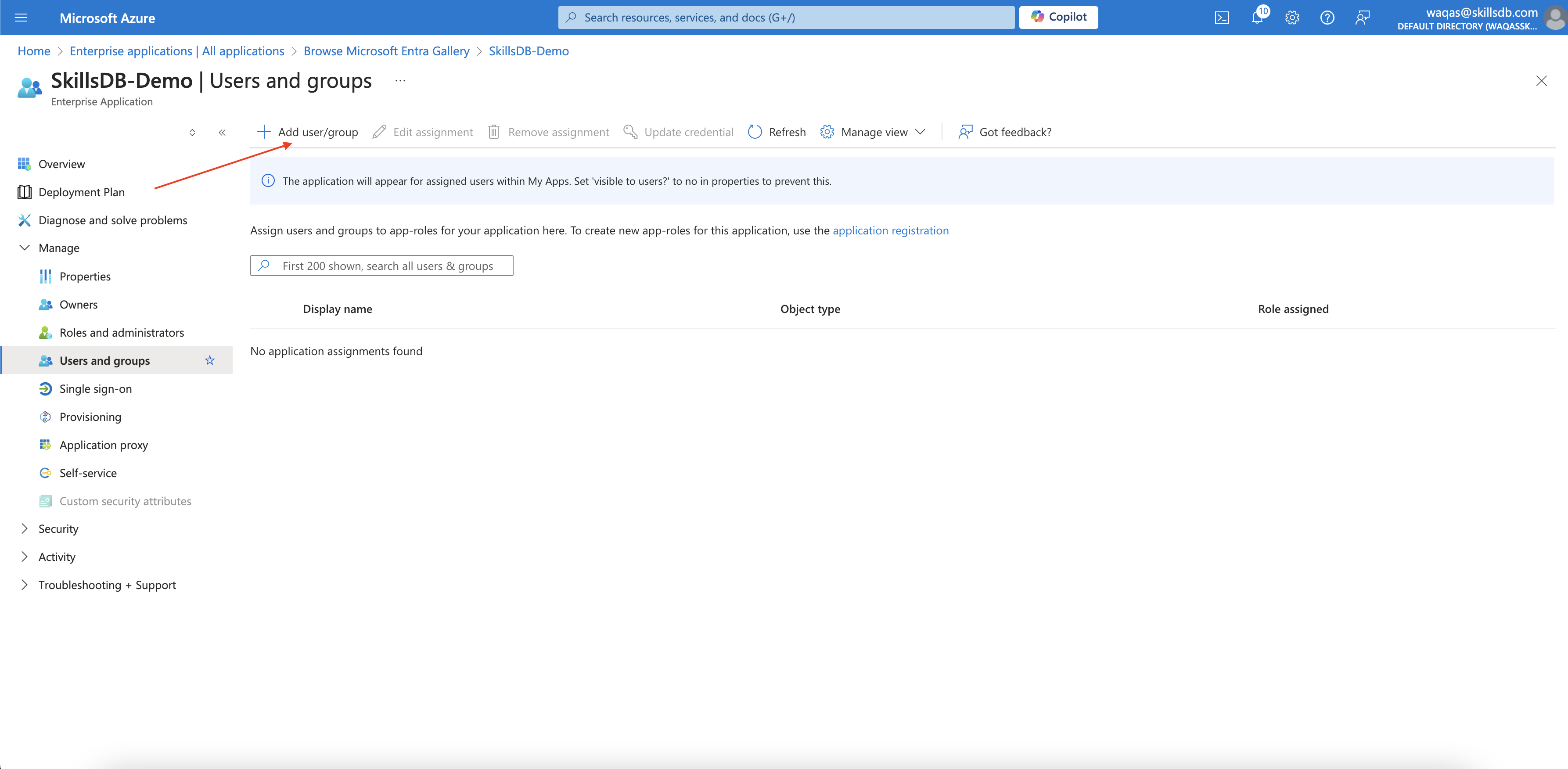
How to assign users to the application
Assigning users to the enterprise application controls who can sign in to SkillsDB through SSO.Open Users and Groups
How to test the SSO connection
After the metadata URL or x509 certificate is in place on the SkillsDB side, any user signed in to their Microsoft organization account can test the integration in three ways.Direct Sign on URL
Open the Sign on URL that SkillsDB Support provided. The URL routes the user through Entra and back into SkillsDB.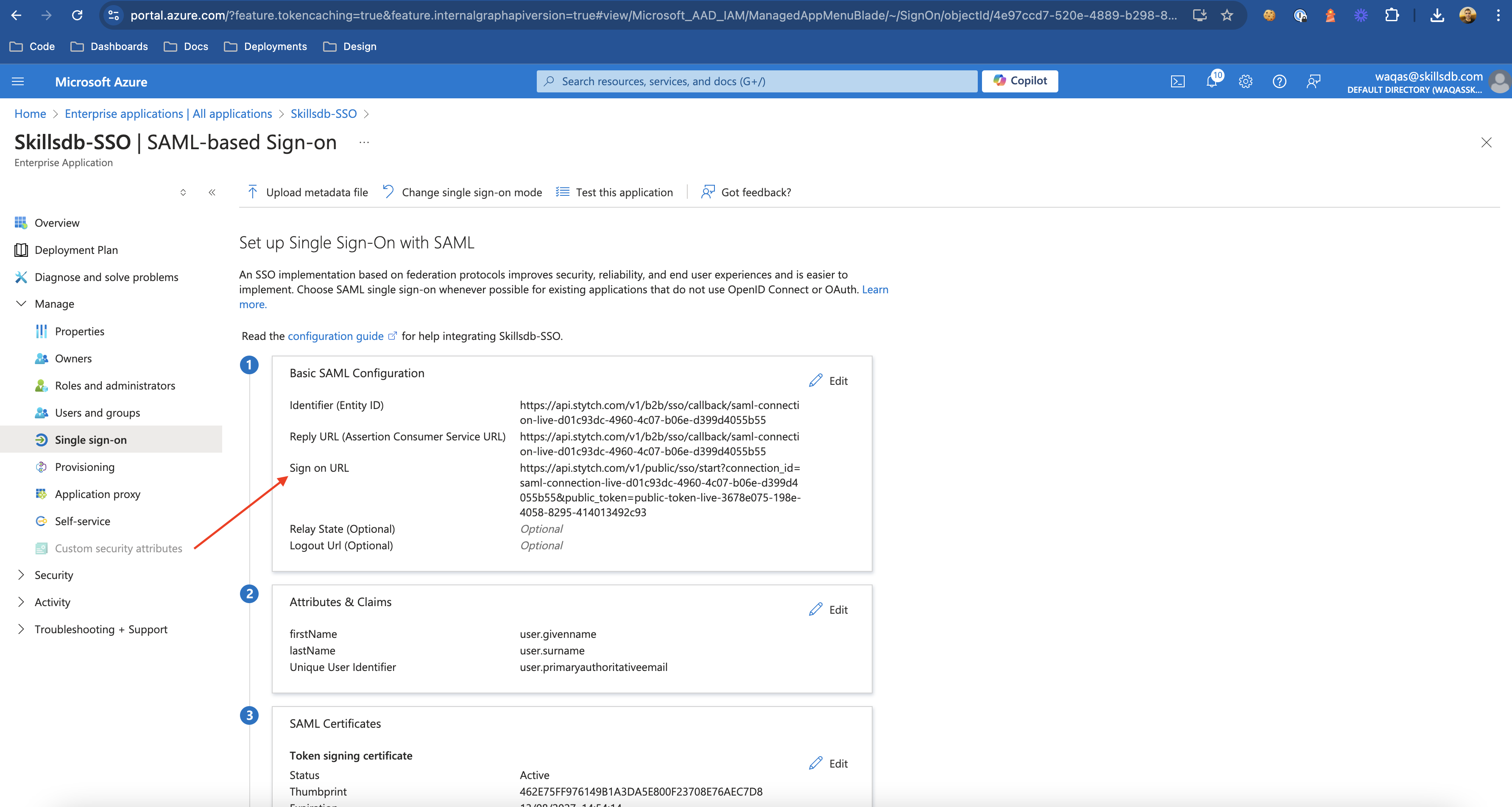
Microsoft My Apps portal
Navigate to https://myapplications.microsoft.com/ and select the SkillsDB enterprise application tile.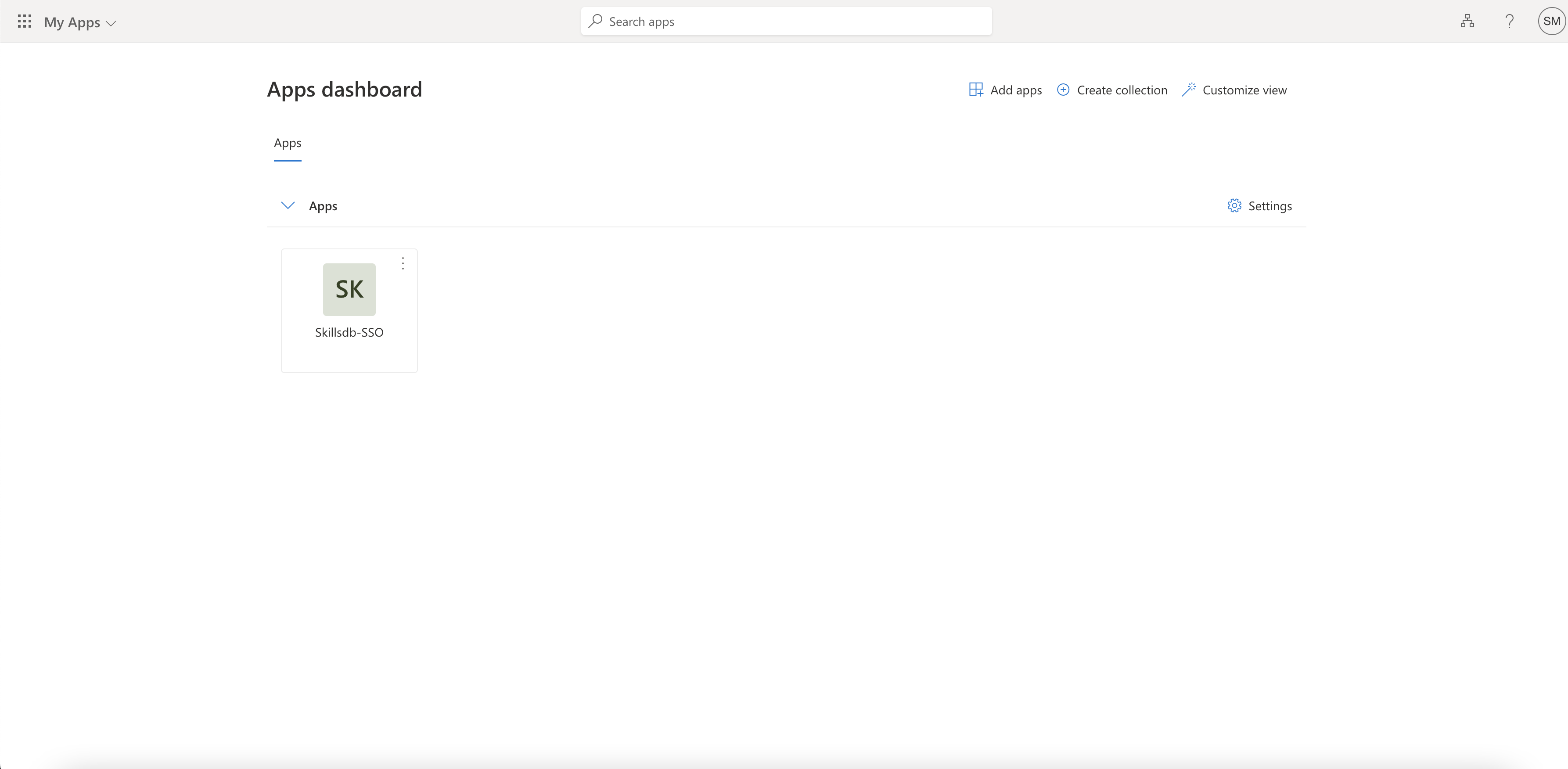
Test from the Azure portal
An administrator already provisioned in SkillsDB can validate the connection from the Entra application itself:- On the application’s Single sign-on page, select Test
- Choose Sign in as current user to verify your own session, or Sign in as someone else to test on behalf of another user
 In all three flows, the user briefly sees an authenticating screen before landing in SkillsDB.
In all three flows, the user briefly sees an authenticating screen before landing in SkillsDB.
Common Questions
Do I need SCIM if I have SSO configured?
Do I need SCIM if I have SSO configured?
Why does SkillsDB use Stytch for SSO?
Why does SkillsDB use Stytch for SSO?
Can I use the App Federation Metadata URL after I have already sent an x509 certificate?
Can I use the App Federation Metadata URL after I have already sent an x509 certificate?
What happens if a user signs in through SSO but does not yet have a SkillsDB account?
What happens if a user signs in through SSO but does not yet have a SkillsDB account?
My users are getting an SSO error after sign-in. What should I check?
My users are getting an SSO error after sign-in. What should I check?
NameID, firstName, lastName) are present and that NameID resolves to the user’s email. If both are correct and the issue persists, contact SkillsDB Support with the timestamp of the failed attempt so they can review the SSO logs in Stytch.Can I send additional attributes beyond email, first name, and last name?
Can I send additional attributes beyond email, first name, and last name?
Department or JobTitle — and notify SkillsDB Support of the exact claim Names. SkillsDB Support extends the mapping in Stytch so the additional values flow through on each sign-in.What test environment URLs should I use during pre-production setup?
What test environment URLs should I use during pre-production setup?
https://test.stytch.com/* instead of https://login.skillsdb.com/* for the Identifier, Reply URL, and Sign on URL. SkillsDB Support sends the correct values for your environment in the SAML endpoint file.